The information provided by website should be used for educational purpose only, website will not be held responsible in the event any criminal charges be brought against any individuals misusing the information in this website to break the law.
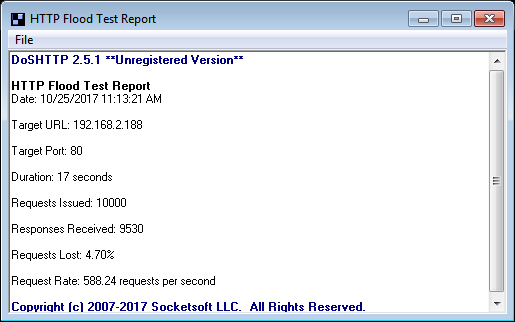
 The Test report will be generated.
The Test report will be generated.
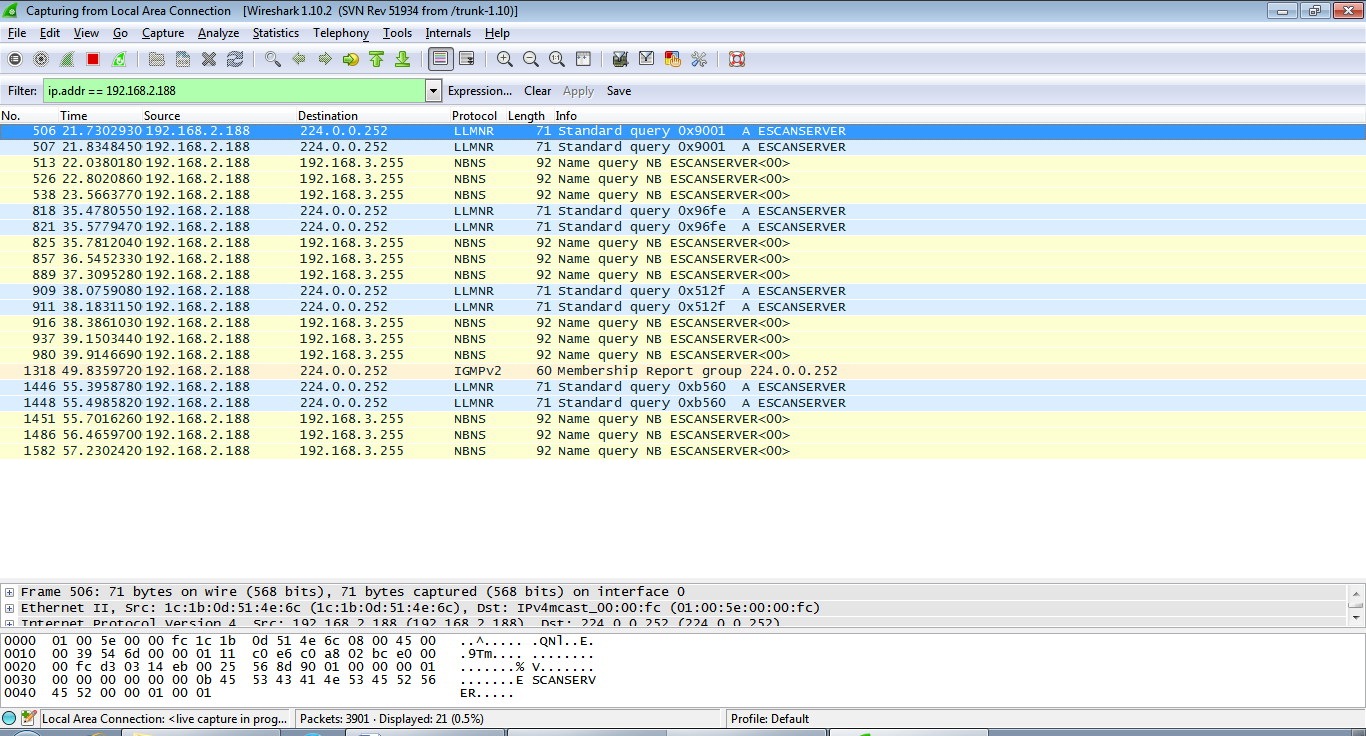
 Check the output whether it is really happening using wireshark.
Check the output whether it is really happening using wireshark.