


Memory is the most important part of a computer for storing data. It is important to address this in a computer system because the amount of main memory in a computer system is very limited. There are so many things competing for it every time. Additionally, multiple processes are performed simultaneously to maximize efficiency. This requires a lot of main memory, so it’s even more important to maintain it.
The role of memory control
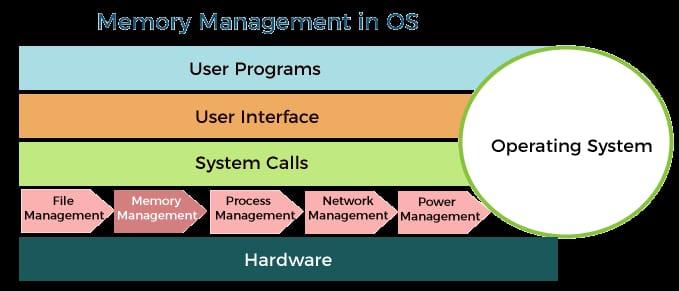
Following are the important functions of memory management in a computer system.
1. The memory manager is used to track the status of memory locations, whether they are freed or shared. The allocation of abstraction handles initial memory so that the software assumes that it is allocated large amounts of memory.
2. The memory manager enables computers with limited main memory to execute programs larger than the size or amount of available memory. It does this by moving information back and forth between primary and secondary memory through the concept of exchange.
3. The memory manager is responsible for protecting the memory allocated to each task from corruption by other tasks. If care is not taken, the system may exhibit unpredictable behavior.
4. Memory managers should provide sharing of memory space between processes. Thus, two activities can reside in the same memory location even at different times.
Memory management methods:
Memory control methods can be divided into the following main categories.
1. Contiguous Memory Management System
2. Non-contiguous memory management systems
1. Contiguous Memory Management System:
In Contiguous memory management scheme each program contains a connected block of storage locations ie. memory locations with consecutive addresses
2. Non-contiguous Memory Management system:
In a Non-Contiguous memory management system, the program is divided into blocks and placed in sections of memory that do not need to be adjacent to each other This system can divide this system based on the size of the blocks, whether blocks resides in main memory or not .
Div-A
Deepti Ghori
53003230075