


Introduction to Data Science: Life Cycle & Applications
Data Science is the process of collecting, cleaning, analyzing, and interpreting data to extract useful
insights for decision-making. It plays a key role in business, healthcare, finance, and modern
technology.
1.Why It’s Important
* Understand customer needs
* Predict sales and trends
* Detect fraud and risks
* Power modern apps & services
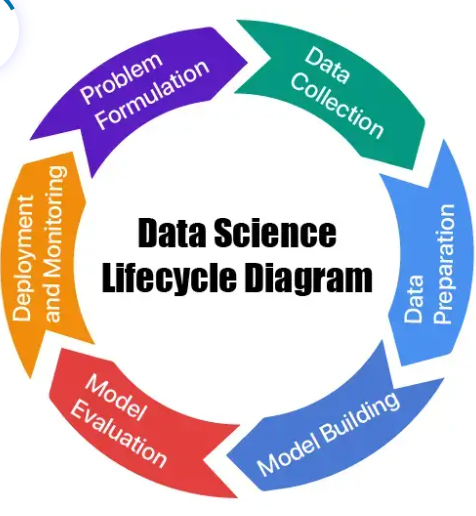
2.Data Science Life Cycle
1. Collect Data – from apps, sensors, web
2. Clean Data – remove errors, organize
3. Explore Data – find patterns & trends
4. Analyze Data – apply statistics & ML
5. Visualize & share – charts, dashboards
6. Decision Making – improve business outcomes
3.Applications
* Healthcare → disease prediction, treatment suggestions
* E-commerce → product recommendations (Amazon, Flipkart)
* Entertainment → movie & music suggestions (Netflix, Spotify)
* Finance → fraud detection, risk management
4.Conclusion
Data Science turns raw data into actionable knowledge. It drives innovation, efficiency, and smarter
decisions across industries — truly making data the new oil.