


We are living in digital world where technology develops day by day.Internet is affordable and electronic devices are also not costly,so criminals are also using digital platforms for criminal/illegal activities.
Types of Cybercrime -
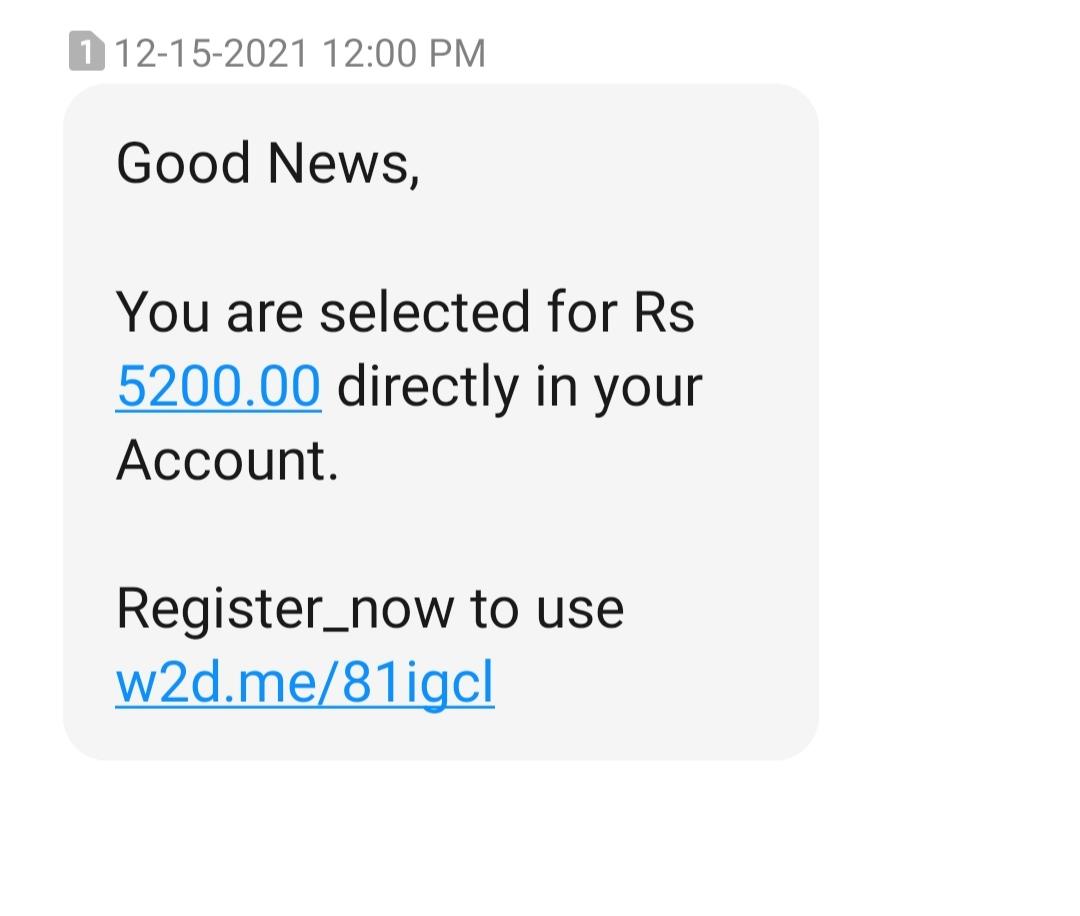
Online Money ask - it is attempt to scam people by giving them false hope/promises
People who need employment are very easily fell into traps
Fraudster tell you to pay amount for interview or other things like enroll for next hiring
Lottery ,jackpot, direct money into account like this promises are scammers doing
Then they will block or didn’t gave you reply
Sextortion -
It is blend of sex+extortion.It is similar to online blackmail
It is modern term and growing faster through social media
Basically teenagers and younger peoples are fell into this easily
Victim got dm/msg then asking for video call for revealing their private/sensitive information or exchange of naked images or videos.Then they store that data and blackmailing victim to pay extortion or do other activity
Phising - it is type of fraud that involves stealing personal information such as login id & password , credit/debit card information etc
Attacker will send mail/link that looks like similar as original website
Vishing - it is attempt where fraudsters try to seek personal information like id,password,atm pin,debit/credit card info or pin otp through call
Smishing - it is fraud that uses text msg/mail to lure victims into call innocent people,visiting harmful websites or downloading malicious content
Ransomware - Ransomeware is type of computer malware that encrypt the files,storage mediaon devices like smartphones,computer,laptops etc. Victim is asked to pay demanded ransom for decryption of device
Data breach - In this Database information is leaked by anonymous/unauthorized person.
Domino's , Mobikwik,Air India's data breach is also done recently