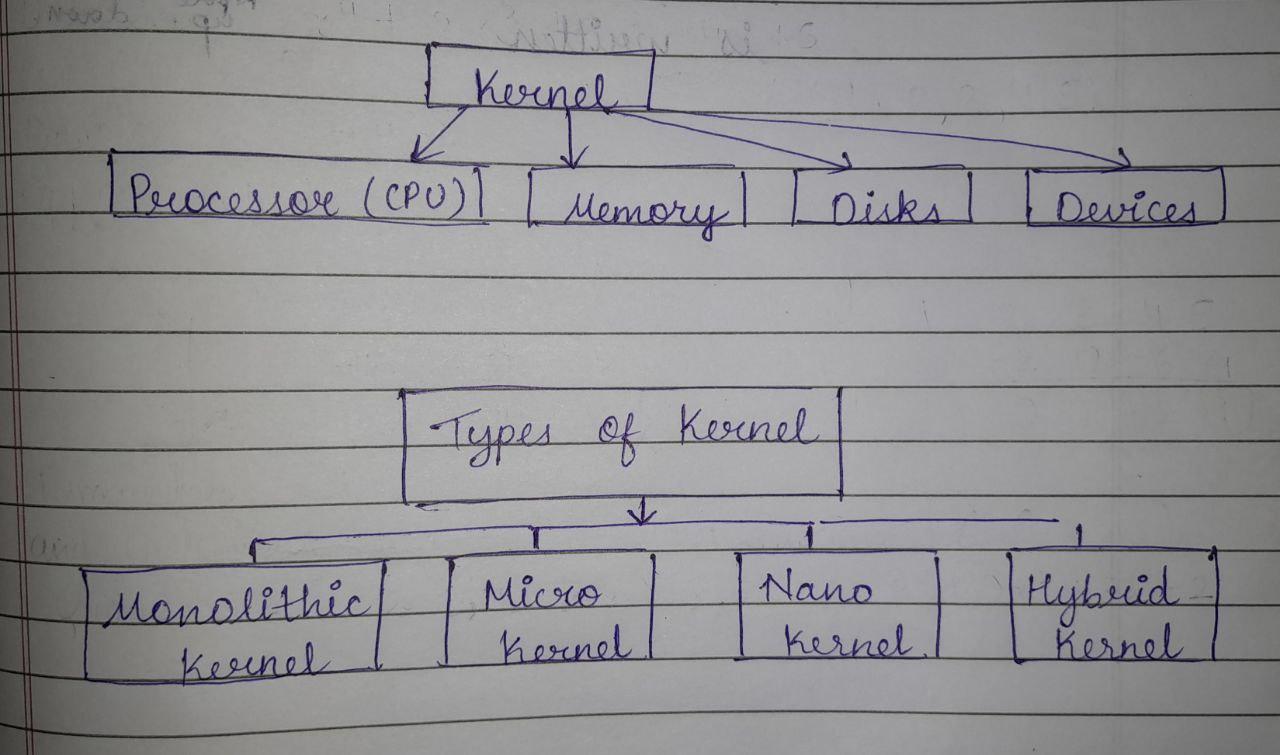
Kernel is the main component of the Operating systems. Its main task is to basically manage the operations of the memory and CPU time. It loads to begin with into memory when an working framework is stacked and remains into memory until working framework is closed down once more. It is accountable for managing tasks such as Disk Management , task Management and Memory Management. It focuses to manage commuication between software and disk memory. It acts as a bridge between applications and data processing done at the hardware level. It is the central component of an OS.
Types of Kernel :
1. Monolithic Kernel :-
- It operates on the kernel space as communication is more efficient .
- It is faster than other types of kernel as it don’t switch between users and kernel modes.
- It has lower inactivity than other sorts of bits since framework calls and hinders can be taken care of specifically by the kernel.
- It is simpler and easy to design.
- Example :- Unix , Linux
2. Micro Kernel :-
- It is more flexible as it allows different OS services to be added or removed without affecting the entire system.
- It is more portable as it is easier to port the operating system to different hardware architectures.
- Example :- Mach , L4 , etc.
3. Nano Kernel :-
- It is amazingly little, giving as it were the most fundamental capacities required to run the framework.
- It is more quick and productive than other bit sorts.
- It is exceedingly convenient, permitting them to run on a wide run of equipment models.
- Example : - EROS , etc.
4. Hybrid Kernel :-
- It is the combination of both solid part and microkernel.
- It gives better performance as they reduce the number of context switches required between user space and kernel space.
- It more congruous than microkernels since they can bolster a more extensive run of gadget drivers.
- Example :- Windows , NT , MacOS , etc.