Interrupts are critical mechanisms in operating systems that enable the CPU to efficiently respond to and manage events requiring immediate attention. They can be hardware- or software-generated signals, temporarily halting the CPU's current activities to execute an appropriate interrupt service routine (ISR).An interrupt is a signal sent to the CPU by a peripheral device or software indicating that it requires immediate attention. Interrupts temporarily halt the current CPU operations, save its state, and execute a function (interrupt handler or interrupt service routine) to address the event. Once the interrupt is handled, the CPU resumes its previous operations.
Types of Interrupts
- Hardware Interrupts: Generated by external devices like keyboards, mice, network cards, and timers. For instance, pressing a key sends an interrupt to the CPU, prompting it to read the keystroke.
- Software Interrupts: Triggered by software instructions, such as system calls requesting OS services or exceptions like division by zero.
- Maskable and Non-Maskable Interrupts: Maskable interrupts can be disabled by the CPU, while non-maskable interrupts (NMIs) are critical and cannot be ignored, often used for urgent tasks like hardware failure alerts.
Interrupt Handling Process
- Interrupt Request (IRQ): A device sends an interrupt signal to the CPU.
- Interrupt Acknowledgment: The CPU acknowledges the interrupt, saving the current state.
- ISR Execution: The CPU executes the relevant ISR.
- State Restoration: The CPU restores the saved state and resumes its prior activities.
Benefits
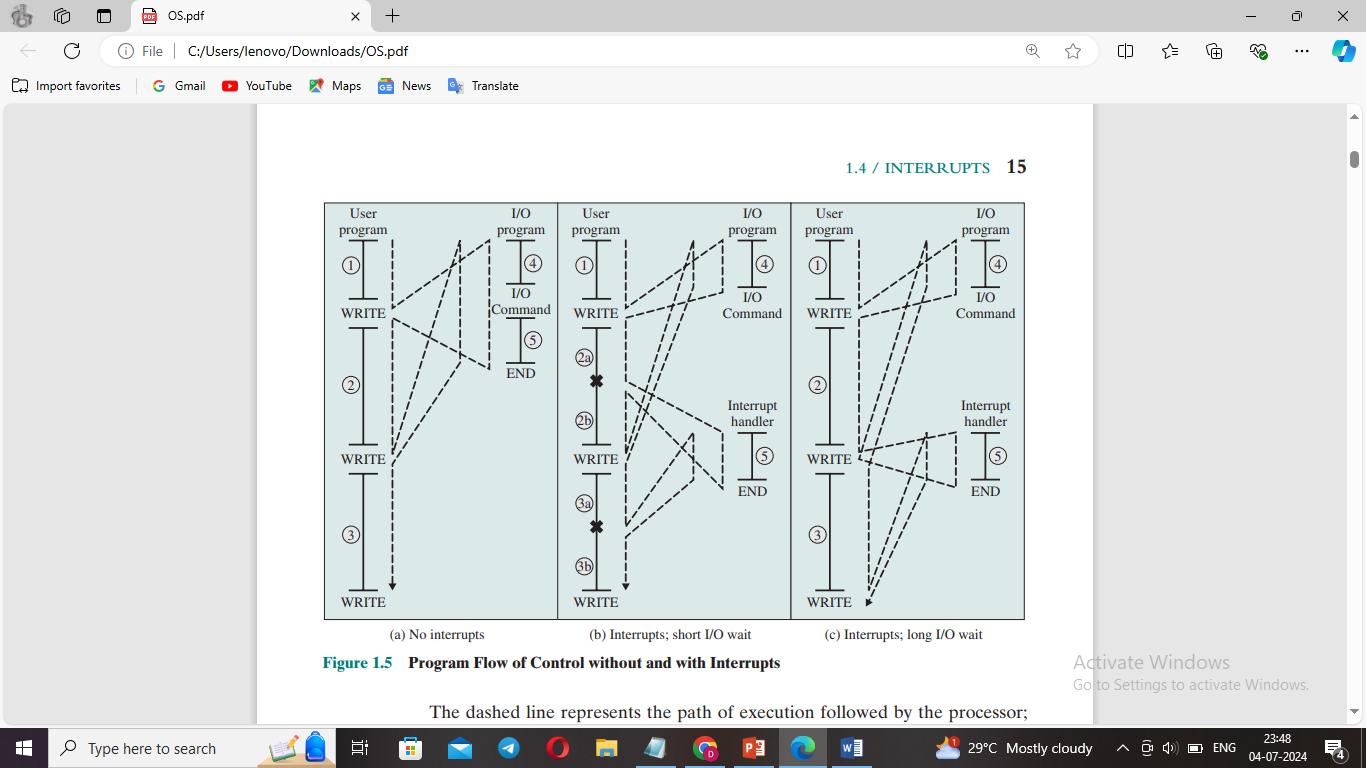
- Efficient CPU Utilization: Interrupts allow the CPU to perform other tasks while awaiting events, avoiding constant polling.
- Real-Time Processing: Ensures timely response to critical events, crucial for real-time systems.
- Enhanced Multitasking: Facilitates efficient process scheduling, distributing CPU time among tasks.
- Improved Error Handling: Catches and manages exceptions gracefully.
Implementation
Operating systems use an Interrupt Vector Table (IVT) to map interrupt types to their corresponding ISRs. Prioritization schemes ensure more critical interrupts are handled first, optimizing system responsiveness and stability.
Conclusion
Interrupts are indispensable for modern OS functionality, enabling responsive, efficient, and multitasking computing environments. They allow the CPU to address urgent tasks promptly, ensuring smooth and effective system operations.