


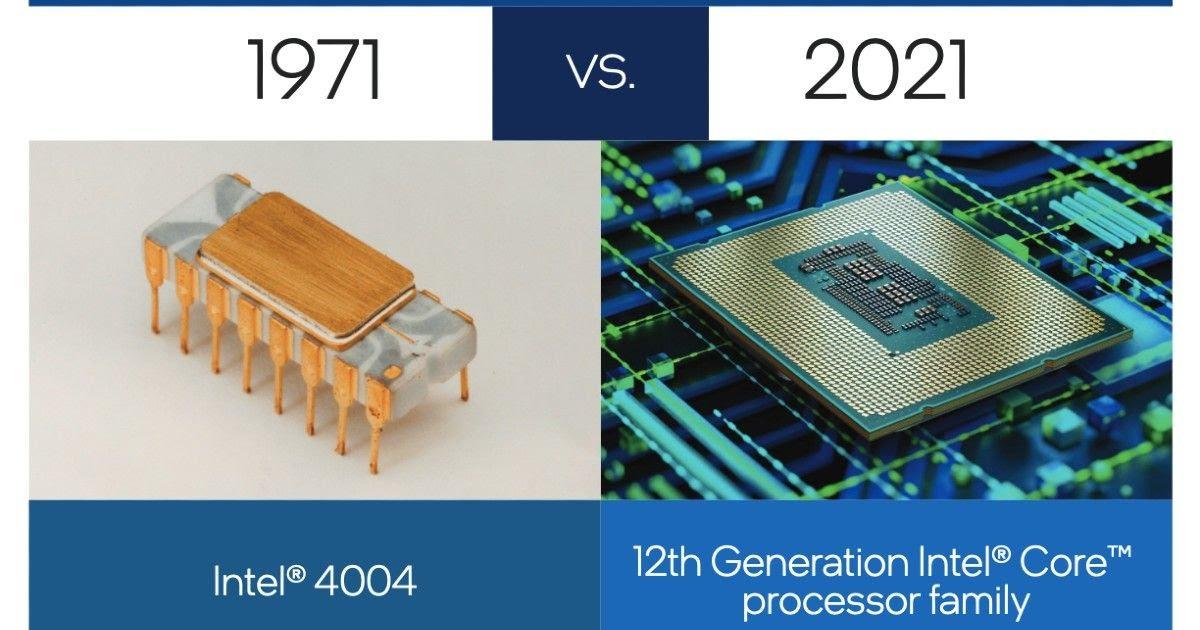
The hardware revolution that brought about desktop and handheld computing was
the invention of the microprocessor, which contained a processor on a single chip.
Though originally much slower than multichip processors, microprocessors have
continually evolved to the point that they are now much faster for most computa-
tions due to the physics involved in moving information around in sub-nanosecond
timeframes.
Not only have microprocessors become the fastest general purpose processors
available, they are now multiprocessors; each chip (called a socket) contains multi-
ple processors (called cores), each with multiple levels of large memory caches, and
multiple logical processors sharing the execution units of each core. As of 2010, it is
not unusual for even a laptop to have 2 or 4 cores, each with 2 hardware threads, for
a total of 4 or 8 logical processors.
Although processors provide very good performance for most forms of
computing, there is increasing demand for numerical computation. Graphical
Processing Units (GPUs) provide efficient computation on arrays of data using
Single-Instruction Multiple Data (SIMD) techniques pioneered in supercomput-
ers. GPUs are no longer used just for rendering advanced graphics, but they are
also used for general numerical processing, such as physics simulations for games
or computations on large spreadsheets. Simultaneously, the CPUs themselves are
gaining the capability of operating on arrays of data—with increasingly power-
ful vector units integrated into the processor architecture of the x86 and AMD64
families.
Processors and GPUs are not the end of the computational story for the
modern PC. Digital Signal Processors (DSPs) are also present, for dealing with
streaming signals—such as audio or video. DSPs used to be embedded in I/O
devices, like modems, but they are now becoming first-class computational devices,
especially in handhelds. Other specialized computational devices (fixed function
units) co-exist with the CPU to support other standard computations, such as
encoding/decoding speech and video (codecs), or providing support for encryption
and security.
To satisfy the requirements of handheld devices, the classic microprocessor
is giving way to the System on a Chip (SoC), where not just the CPUs and caches
are on the same chip, but also many of the other components of the system, such as
DSPs, GPUs, I/O devices (such as radios and codecs), and main memory.