


Memory management in an operating system (OS) is vital for optimizing a computer's use of its memory resources, ensuring processes run efficiently and reliably. It involves several key functions:
1. Memory Allocation:The OS allocates memory to processes either statically (at compile time) or dynamically (at runtime). Static allocation is fixed and determined before the program runs, whereas dynamic allocation adjusts as processes require more or less memory during execution, offering greater flexibility but needing careful management.
2. Paging and Segmentation: To handle memory efficiently, OSs use paging and segmentation. Paging divides memory into fixed-size blocks called pages and maps virtual addresses to physical addresses using a page table. This approach minimizes fragmentation and allows for more flexible memory use. Segmentation, on the other hand, divides memory into variable-sized segments based on logical divisions like code, data, and stack, simplifying management and addressing different data types more efficiently.
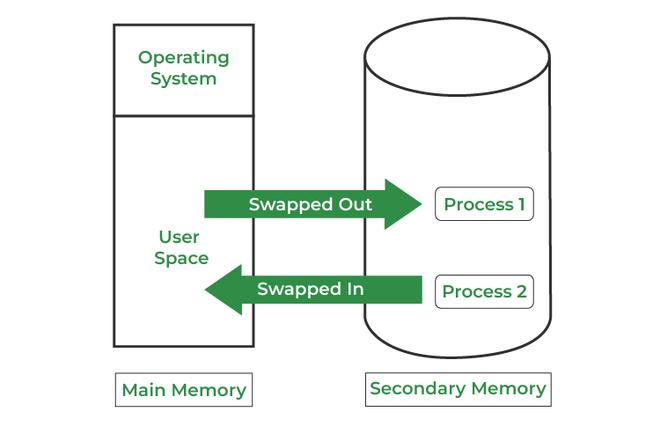
3. Virtual Memory: Virtual memory extends the apparent amount of RAM by using disk space to simulate additional memory. This technique allows the system to run more processes concurrently by swapping data between RAM and disk storage, creating the illusion of a larger memory space and handling large applications effectively.
4. Memory Protection and Sharing: Memory protection prevents processes from interfering with each other's memory, maintaining system stability and security through address space isolation and access control mechanisms. Memory sharing allows multiple processes to access common memory regions, facilitating inter-process communication and efficient resource use.
5. Garbage Collection: In some systems, particularly those with managed languages like Java, garbage collection is used to automatically reclaim memory that is no longer needed. This process helps prevent memory leaks, where unused memory is not freed, thus improving overall resource efficiency.
6. Fragmentation Handling: Fragmentation occurs when memory is divided into non-contiguous blocks. External fragmentation happens with scattered free memory, while internal fragmentation involves unused space within allocated blocks. The OS may use compaction to address these issues by reorganizing memory to reduce fragmentation and consolidate free space.
Overall, memory management ensures that the system uses memory resources effectively, balancing between allocation efficiency, protection, and performance.